Target’s corporate network was breached between November 27th, 2013 to December 15th, 2013 that resulted in 110 million credit cards and personal records being stolen. This data breach happened during the busiest days for retailers between the hours of 10:00am to 6:00pm. When I heard about this data breach in the news, I assumed that the attack was so sophisticated that it might have been difficult for Target to preempt it. But as I started to read articles on the breach, it became clear that although the attack used a combination of social engineering, phishing, and malware techniques it was not a sophisticated attack.
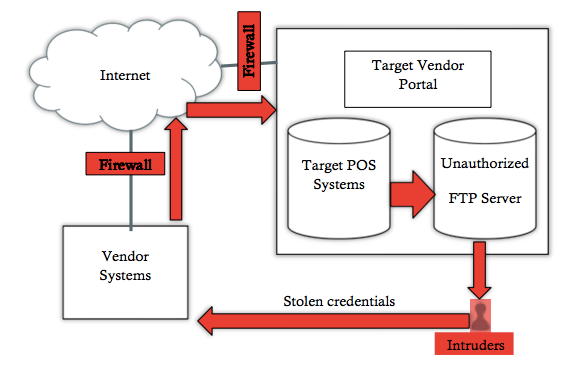
The articles indicate that intruders obtained stolen login credentials from one of Target’s vendors. This vendor accessed information on Target’s intranet via a portal that was set up for Target’s vendors. Once the intruders were able to get into the network, they were able to access Target’s Point-Of-Sale (POS) payment systems. The intruders were able to install malware on these systems that provided them with consumer information.
From a technology perspective, a few gaps that standout include:
- The lack of segmentation of the network to avoid access to payment systems
- The inability to identify data transfers to an unauthorized File Transfer Protocol (FTP) server
- The failure to detect that intruders were testing their malware on a few POS systems before they launched a full attack
- The deliberate ignoring of malware warnings from their internal systems
From a business perspective, a few gaps that standout include:
- The data breach was not made public until Brian Krebs (a blogger) broke the news
- Lack of adherence to security processes and practices
- Too much reliance on just security certifications
The following figure shows the network and the route intruders took to access Target’s POS systems.
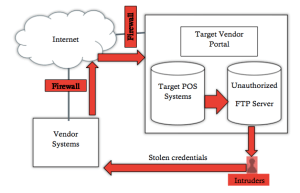
From the figure, we can visualize the multiple issues with Target’s network. Although Target cannot be held accountable for any vulnerabilities caused due to its vendors it should have considered the potential of exploits that may be caused due to its vendors. Since the underlying network was the same, it had to be secure and constantly monitored for systems spikes and unusual network traffic activities. What is interesting about this attack is that although a large number of consumer records were stolen it has not been reported that how many corporate accounts were stolen too. Since 54% of businesses are small in the US, I am sure there have been corporate accounts that have been compromised as well.
As I have looked at what happened in this case, security is a management issue. In Target’s case, its management failed to see beyond their corporate environment and did not see holistically how the business processes that they put in place could be their downfall. Management also failed to inform the consumer. How long management would have waited to inform the consumers? My guess is that if the story had not been leaked, Target management would have conveniently forgotten about it.
In conclusion, there are three broader issues that come to mind (1) organizations are only as strong as their weakest link especially when that link is the corporate network (2) although organizations provide credit monitoring typically for a year but they assume that the intruders would only use this exploited information for a year and (3) consumers are left to fend for themselves during and after the one year period when their credit scores decline. In short, these data breaches have to be significantly eliminated since they not only cause loss of reputation but also loss of consumer confidence in an organization’s role as the protectors of our data. This is possible by not only credentialing but repetitively checking various ways how systems can be exploited from within and external to the organization even if the underlying network is perceived to be secure.
References:
http://blogs.wsj.com/corporate-intelligence/2013/12/27/targets-data-breach-timeline/
Click to access Target_Kill_Chain_Analysis_FINAL.pdf
http://krebsonsecurity.com/2013/12/sources-target-investigating-data-breach/
http://www.sba.gov/offices/headquarters/ocpl/resources/13493

You must be logged in to post a comment.